Introduction
In today’s hyperconnected world, securing your Linux servers is not optional, it’s essential. Whether you're hosting a small website or managing a large-scale cloud infrastructure, server hardening is the first line of defense against cyber threats. At COLO BIRD, we prioritize performance, flexibility, and security. In this blog, we walk you through the importance of Linux server hardening and offer a comprehensive checklist to improve your system’s resilience.
Understanding Web Servers and Their Types
A web server is a program that serves web pages using the HTTP protocol in response to client requests. Popular web servers include Apache and Microsoft IIS. Today, websites are vital to every organization, serving as digital storefronts and communication platforms.
Web applications are hosted using platforms like:
- LAMP: Linux, Apache, MySQL, and PHP/Perl/Python
- WAMP: Windows, Apache, MySQL, and PHP
When it comes to hosting environments, there are three major types of Linux-based servers:
- Shared Servers
- Virtual Private Servers (VPS)
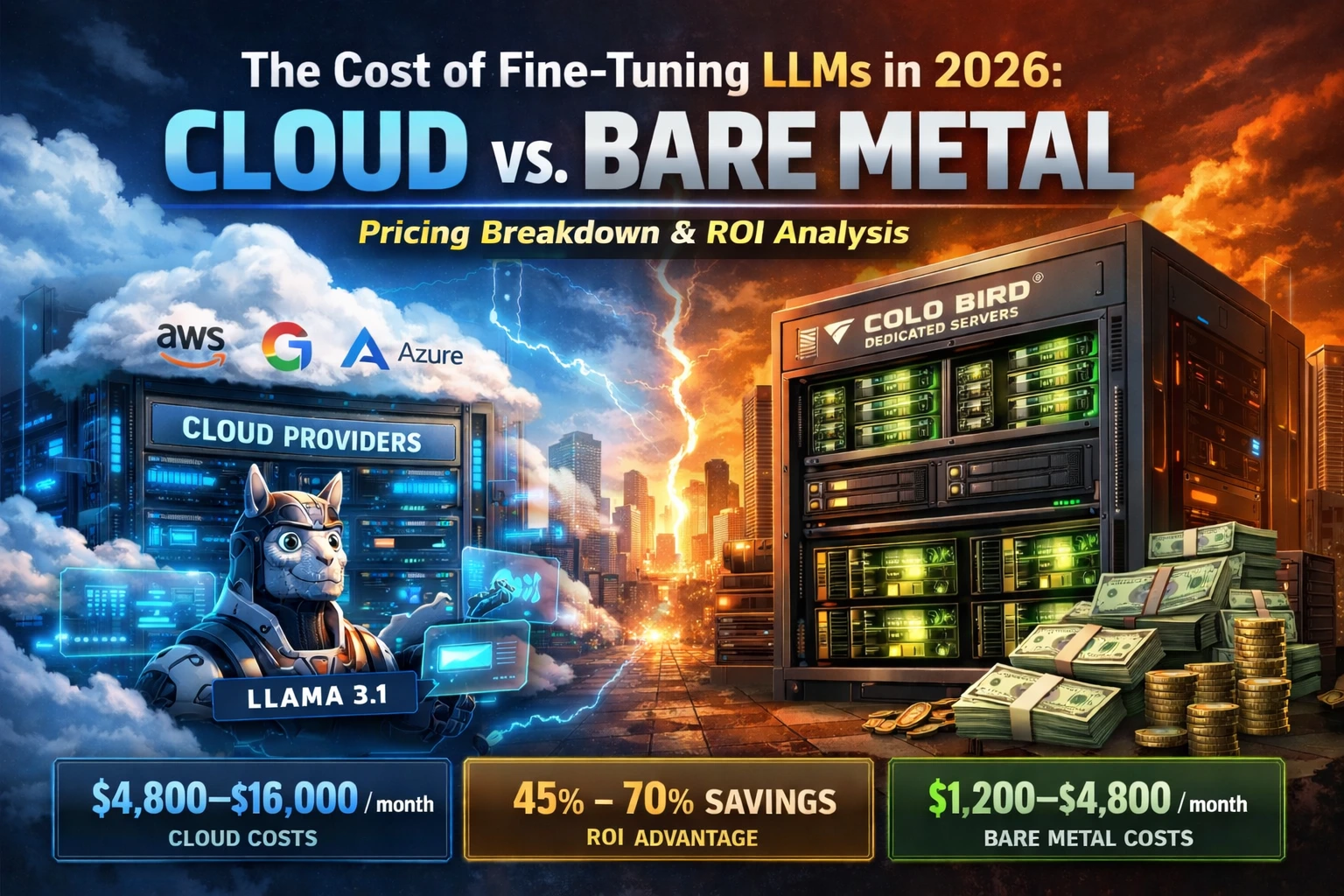
- Cloud Servers (e.g., AWS, OpenStack, Rackspace)
Cloud servers, in particular, offer scalability and automation, making them the preferred choice for modern businesses.
Why Linux Server Hardening is Crucial
Threats like ransomware highlight the importance of proactive server protection. Ransomware locks users out of their data and demands payment to restore access. Often, these attacks exploit unprotected or poorly configured systems.
Unfortunately, default Linux installations are not optimized for security. Without hardening, your server may be an easy target for hackers.
Server Hardening Checklist: Security Best Practices for Linux
Here’s a curated list of essential steps you can take to harden your Linux server:
-
1.Disable Ctrl+Alt+Delete
Prevent physical reboot attempts by commenting out the following line in older systems (like CentOS 6):
ca::ctrlaltdel:/sbin/shutdown -t3 -r now -
2.Disable Direct Root Login and Create a Dedicated SSH User
The root account has full privileges; avoid using it directly. Instead:
- Create a separate user with sudo privileges.
- Disable root login in /etc/ssh/sshd_config:
PermitRootLogin no -
3.Change Default SSH Port and Disable ICMP Ping
Allows or blocks traffic based on state, port, and protocol. It uses rules set by the administrator and the context of the traffic.
- Modify /etc/ssh/sshd_config to use a non-standard port (e.g., 2222).
- Disable ping (ICMP requests) by editing /etc/sysctl.conf:
net.ipv4.icmp_echo_ignore_all = 1Apply changes with sysctl -p.
-
4.Set Up CSF Firewall
ConfigServer Security & Firewall (CSF) is a powerful SPI firewall. It helps:
- Restrict access by IP
- Detect login attempts
- Prevent port scans
-
5.Install mod_evasive and mod_security
Protect Apache with:
- mod_evasive: Blocks DoS and brute-force attacks.
- mod_security: Web application firewall that filters and sanitizes HTTP requests.
-
6.Scan with Rootkit Hunter (rkhunter)
Detect rootkits and backdoors with:
rkhunter --checkIt checks for:
- MD5 hash anomalies
- Hidden files
- Insecure permissions
- Suspicious strings in kernel modules
-
7.Run Malware Scans with Maldet and ClamAV
Use Linux Malware Detect (Maldet) and ClamAV to scan and eliminate malware, trojans, and suspicious scripts.
maldet -a /homeclamscan -r /home -
8.Automate Weekly ClamAV Scans with Cron
Schedule weekly scans and automatic updates using a cron job:
0 3 * * 0 freshclam && clamscan -r / --log=/var/log/clamav/weekly.log -
9.Hide Apache and PHP Version Information
Remove software version details to avoid giving clues to attackers:
- Apache: Set ServerTokens Prod and ServerSignature Off
- PHP: In php.ini, set:
expose_php = Off -
10.Disable FTP — Use SFTP Instead
FTP is insecure and often exploited. Switch to SFTP, which is encrypted via SSH. Tools like WinSCP make SFTP easy to use on Windows.
-
11.Restrict Shell Access for Unknown Users
Lock down user shells:
usermod -s /sbin/nologin usernameReview /etc/passwd to identify and disable unknown users.
-
12.Install Fail2Ban to Protect SSH
Fail2Ban monitors login attempts and bans IPs showing malicious behavior. This is essential for preventing brute-force SSH attacks.
Final Thoughts
Initial hardening is just the beginning. As threats evolve, regular security audits, software updates, and vulnerability scans are essential to keep your server secure.
At COLO BIRD, we recommend staying informed about the latest developments in Linux server security. Subscribe to reputable blogs, monitor advisories, and follow best practices.
Your server is only as strong as its weakest link. Secure it today to protect your data, customers, and reputation.